As network activities become more and more complex, enterprise systems and host environments are often subject to unauthorized access or other information security risks due to improper management and settings, and hackers exploit known system vulnerabilities to become a hidden crisis for enterprises.
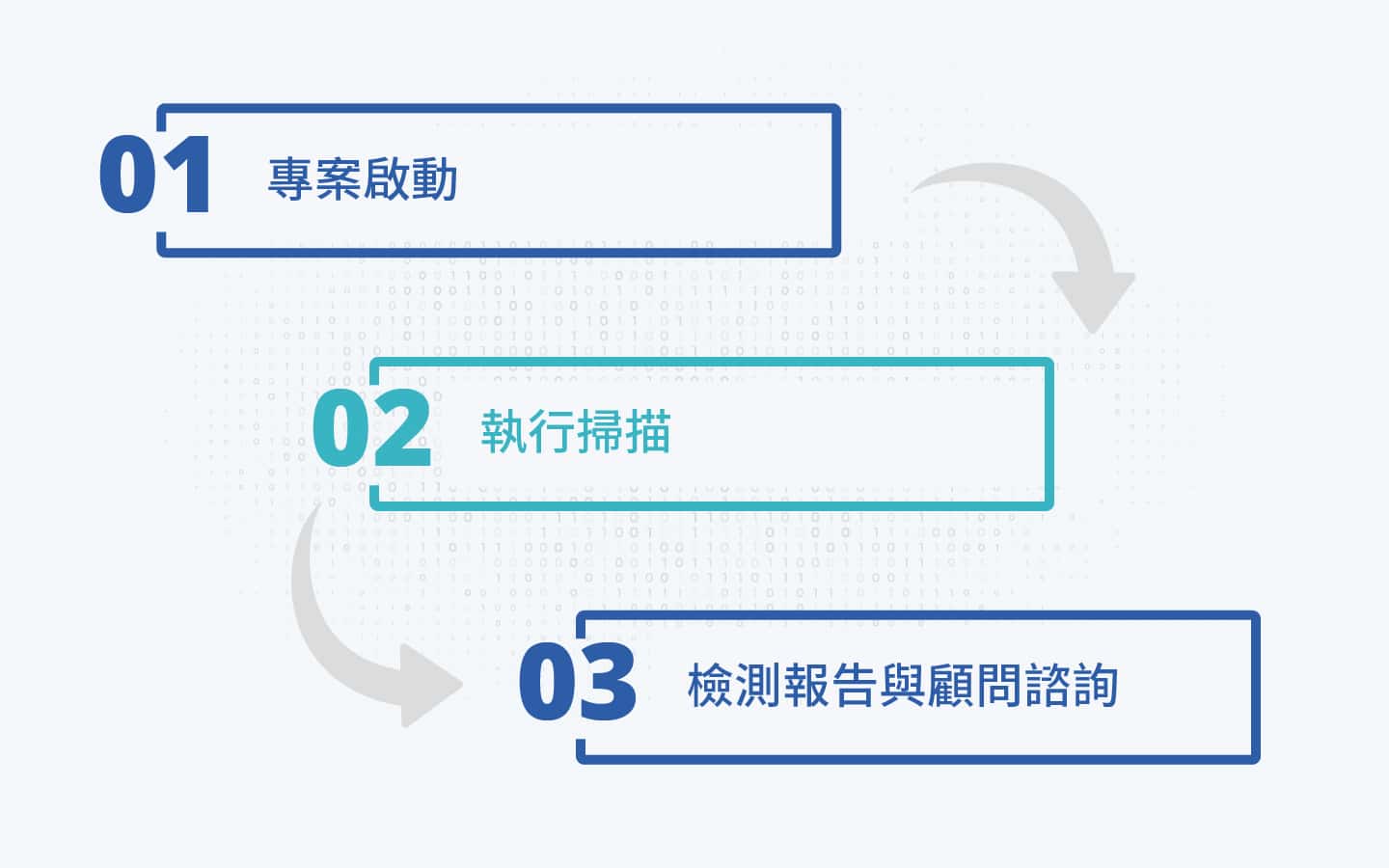
Host Vulnerability Scanning Service is a vulnerability scanning tool that, together with other commonly used tools and commands, helps customers scan various network devices and system hosts in the network environment to quickly identify and fix vulnerabilities, including software vulnerabilities, missing patches, malware, and misconfigurations. Through professional result analysis, we can provide customers with effective and feasible improvement solutions. By scanning for vulnerabilities, we can identify security vulnerabilities in system maintenance early and complete the repair operation in time to avoid intrusion attacks through vulnerabilities, so as to achieve the goal of reducing information security risks.
ISSDU professional inspection team, all of whom have extensive experience in information security and have obtained many international information security licenses, provides professional inspection planning and services to our customers

Chinese scan results report, including the number and ratio of risk vulnerabilities, the total number of vulnerabilities of each type of statistics, the list of vulnerabilities found in each host, and complete patching recommendations
Helps enterprises understand the vulnerability status of various network devices, systems and hosts in their existing environment, and obtain effective improvement solutions through the vulnerability scan results analysis report

According to the needs of different systems, equipment, network segments, categories or importance of the customer, we will tailor a suitable scanning policy and execute the scanning by our own staff

We provide professional inspection reports and remediation recommendations based on the inspection results, and professional consulting services to help corporate customers reduce website security risks