Distributed Denial of Service (DDoS) is a blocking attack against the "availability" of the three elements of information security, combining multiple computers to launch a traffic blocking attack to consume the network bandwidth and system resources of the attack target, making it impossible to provide normal services to the outside world.
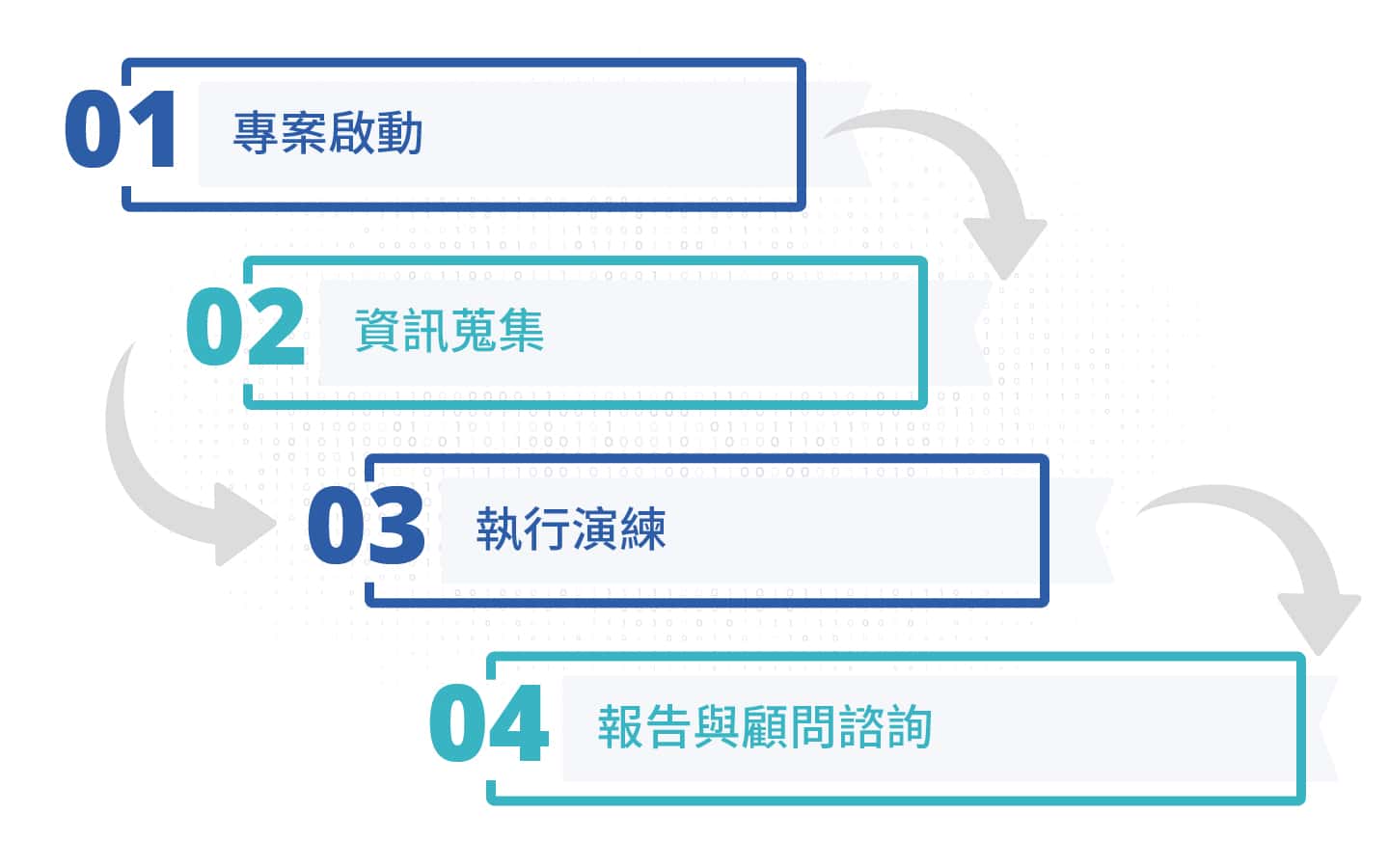
In recent years, because our government agencies and important livelihood service websites have been repeatedly subjected to DDoS attacks by hacker organizations, resulting in the suspension of some websites of the government agencies. The DDoS simulation exercise provides customers with a realistic and controlled attack exercise service to help customers understand the tolerance level of DDoS attacks on current websites or important hosts and design protection solutions to block DDoS attacks.
ISSDU professional testing team, with rich experience in simulation services, helps customers to complete simulation services in a secure environment. Customers cover the financial industry, government, technology industry and manufacturing industry, etc.
Through the independent research and development of the attack system of ISSDU Information Security, the target simulation consumes network bandwidth, system resources and application resources to help customers understand the tolerance of important hosts and network bandwidth to DDoS attacks
The source of the attack is all legal IP, and use legal and safe hosts to execute detection, without affecting enterprise operation, simulate real DDoS attack behavior

The simulation can assist customers to review the deficiencies of the existing architecture, and provide professional report analysis and advice, customize the design of protection solutions to block future DDoS attacks in response to the detection results.